Kubernetes: Port,Targetport and NodePort
by Anish
Posted on Tuesday August 15, 2018
Multiple Port Services
-
Many
Servicesneed to expose more than one port. Kubernetes supports multiple port definitions on aServiceobject. When using multiple ports you must give all of your ports names, so that endpoints can be disambiguated. For example, this definition is used in nginx secure deployment in my previous articleapiVersion: v1 kind: Service metadata: name: nginxsvc labels: app: nginx spec: type: NodePort ports: - port: 80 protocol: TCP name: http - port: 443 protocol: TCP name: https selector: app: nginx
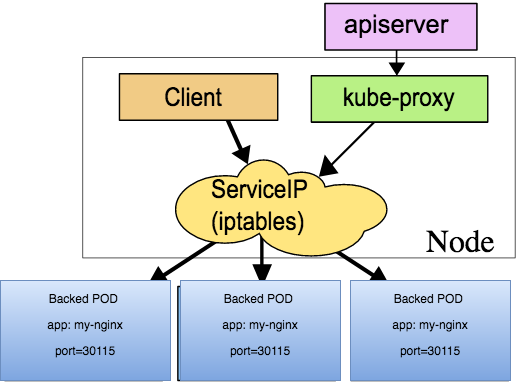
- Port: Port is the port number which makes a service visible to other services running within the same K8s cluster.
- Target Port: Target port is the port on the POD where the service is running.Service can map an incoming port to any targetPort. By default the targetPort will be set to the same value as the port field
- Nodeport: Node port is the port on which the service can be accessed from external world using through Kube-Proxy.In NodePort, the Kubernetes master will allocate a port from a range specified by
--service-node-port-range flag (default: 30000-32767), and each Node will proxy that port (the same port number on every Node) into your Service
-
These are IPtables rules in which will be setup by kubernetes in the master-node.
iptables -t nat --line-numbers -n -L | grep 30287
1 KUBE-MARK-MASQ tcp -- 0.0.0.0/0 0.0.0.0/0 /* default/nginxsvc:https */ tcp dpt:**30287**
2 KUBE-SVC-ER5WGNLE726ZPUG2 tcp -- 0.0.0.0/0 0.0.0.0/0 /* default/nginxsvc:https */ tcp dpt:**30287**
iptables -L | grep 30287
REJECT tcp -- anywhere anywhere /* default/nginxsvc:https has no endpoints */ ADDRTYPE match dst-type LOCAL tcp dpt:**30287** reject-with icmp-port-unreachable
- once the deployment is created , new iptables rules will ge generated, you can find the node port that Kubernetes is using for http and https traffic using the command
kubectl get service nginxsvc -o json
"spec": {
"clusterIP": "10.103.250.179",
"externalTrafficPolicy": "Cluster",
"ports": [
{
"name": "http",
"nodePort": 32210,
"port": 80,
"protocol": "TCP",
"targetPort": 80
},
{
"name": "https",
"nodePort": 30287,
"port": 443,
"protocol": "TCP",
"targetPort": 443
}
],
Further Reading
- Checkout how to deploy HTTPS Secure Nginx deploymet in kubernetes
Thanku for reading !!! Give a Share for Support
Your Support Matters!
Instead of directly asking for donations, I'm thrilled to offer you all nine of my books for just $9 on leanpub By grabbing this bundle you not only help cover my coffee, beer, and Amazon bills but also play a crucial role in advancing and refining this project. Your contribution is indispensable, and I'm genuinely grateful for your involvement in this journey!
Any private key value that you enter or we generate is not stored on this site, this tool is provided via an HTTPS URL to ensure that private keys cannot be stolen, for extra security run this software on your network, no cloud dependency
Kubernetes Related Topics
Linux Related Topics
Ansible Related Topics
Applied Cryptography Topics
Web Crypto API Topics
Openstack Articles
python Cryptography Topics
PHP Cryptography Topics
Topics
For Coffee/ Beer/ Amazon Bill and further development of the project Support by Purchasing, The Modern Cryptography CookBook for Just $9 Coupon Price
Kubernetes for DevOps
Hello Dockerfile